I was reading this stackoverflow comment which describes how rails authenticity tokens work: Understanding the Rails Authenticity Token
and the highest rated response begins with this:
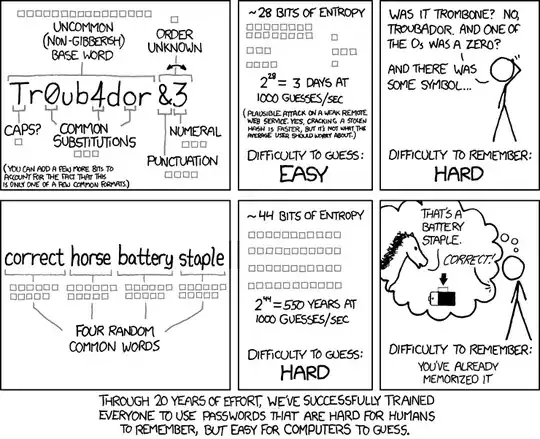
"When the user views a form to create, update, or destroy a resource, the Rails app creates a random authenticity_token, stores this token in the session, and places it in a hidden field in the form. When the user submits the form, Rails looks for the authenticity_token, compares it to the one stored in the session, and if they match the request is allowed to continue."
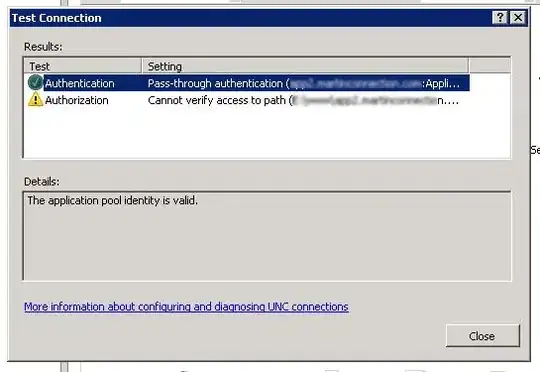
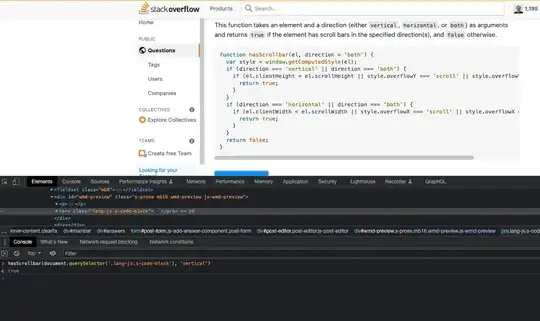
This makes sense to me as an abstract concept but I wanted to understand how this works in a concrete sense, I wanted to see exactly how this happens so I am crystal clear about how this works, so I created a new rails app and scaffolded a User with just one field name then I dropped a binding.pry in Users#create right up top inside the action, which should happen directly after the user submits the form. The pry session began right after I added a new user name, hit submit and it moves to create...So I inspected the source of my application in my web browser to find that the csrf-token content value in my rails generated csrf meta tags do not match the hidden authenticity token value within my form and neither one matches the value I get if, during the same pry session, I examine the session.to_hash property and inspect the "_csrf_token" value.
I then tried setting up a pry in the Users#new action and the Users#create action and noted the "_csrf_token" value on the session and compared it to the values of the form fields and meta tags once I quit and my app moved to the pry in the Users#create action but nothing matched. It seems like none of these three values match at all.
Yet protect_from_forgery with: :exception is set in my application controller and from what I read in the top rated response I was expecting to see matching values...somewhere. It seems like nothing matches. So I currently have no concept of what rails is matching what to in order to allow for the form to proceed and the data to be saved.
The author of the top rated response also says that an authenticity_token is stored on the session but all I see is a _csrf_token (are these the same?) and a session_id and, as I said, they don't match anything. I see no match whatsoever.
If rails is matching something to the value in my form field, it doesn't seem to be the value of the '_csrf_token' unless its converting it to something else behind the scenes and then matching that value to the value in the hidden form field or something. I don't feel like I understand what is going on.