I've OpenSSH 7.6 installed in Windows 7 for testing purposes. SSH client & server work just fine till I tried to access one of my AWS EC2 box from this windows.
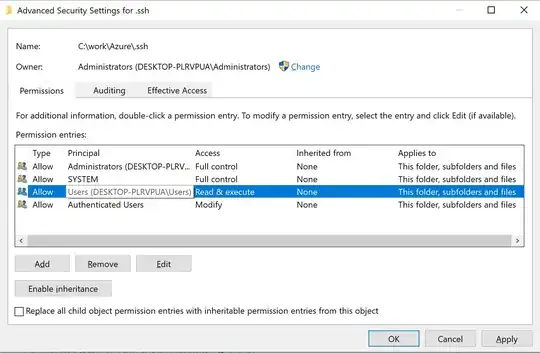
It seems like I need to change the permission on the private key file. This can be easily done on unix/linux with chmod command.
What about windows?
private-key.ppm is copied directly from AWS and I guess the permission too.
C:\>ssh -V
OpenSSH_7.6p1, LibreSSL 2.5.3
C:\>ver
Microsoft Windows [Version 6.1.7601]
C:\>
C:\>ssh ubuntu@192.168.0.1 -i private-key.ppk
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
@ WARNING: UNPROTECTED PRIVATE KEY FILE! @
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
Permissions for 'private-key.ppk' are too open.
It is required that your private key files are NOT accessible by others.
This private key will be ignored.
Load key "private-key.ppk": bad permissions
ubuntu@192.168.0.1: Permission denied (publickey).
C:\>
C:\>
C:\>ssh ubuntu@192.168.0.1 -i private-key.ppm
Warning: Identity file private-key.ppm not accessible: No such file or directory.
ubuntu@192.168.0.1: Permission denied (publickey).
C:\>